212-82 Online Practice Questions and Answers
An IoT device that has been placed in a hospital for safety measures, it has sent an alert command to the server. The network traffic has been captured and stored in the Documents folder of the Attacker Machine-1. Analyze the loTdeviceTraffic.pcapng file and select the appropriate command that was sent by the IoT device over the network.
A. Tempe_Low
B. Low_Tempe
C. Temp_High
D. High_Tempe
Arabella, a forensic officer, documented all the evidence related to the case in a standard forensic investigation report template. She filled different sections of the report covering all the details of the crime along with the daily progress of the investigation process.
In which of the following sections of the forensic investigation report did Arabella record the "nature of the claim and information provided to the officers"?
A. Investigation process
B. Investigation objectives
C. Evidence information
D. Evaluation and analysis process
Riley sent a secret message to Louis. Before sending the message, Riley digitally signed the message using his private key. Louis received the message, verified the digital signature using the corresponding key to ensure that the message was not tampered during transit.
Which of the following keys did Louis use to verify the digital signature in the above scenario?
A. Riley's public key
B. Louis's public key
C. Riley's private key
D. Louis's private key
An FTP server has been hosted in one of the machines in the network. Using Cain and Abel the attacker was able to poison the machine and fetch the FTP credentials used by the admin. You're given a task to validate the credentials that were stolen using Cain and Abel and read the file flag.txt
A. white@hat
B. red@hat
C. hat@red
D. blue@hat
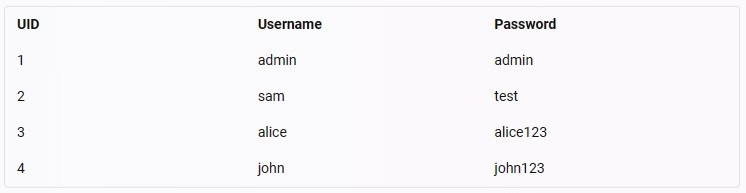
A web application, www.moviescope.com. hosted on your tarqet web server is vulnerable to SQL injection attacks. Exploit the web application and extract the user credentials from the moviescope database. Identify the UID (user ID) of a
user, John, in the database. Note:
Vou have an account on the web application, and your credentials are samAest.
A. 3
B. 4
C. 2
D. 5
Richards, a security specialist at an organization, was monitoring an IDS system. While monitoring, he suddenly received an alert of an ongoing intrusion attempt on the organization's network. He immediately averted the malicious actions by implementing the necessary measures.
Identify the type of alert generated by the IDS system in the above scenario.
A. True positive
B. True negative
C. False negative
D. False positive
Cassius, a security professional, works for the risk management team in an organization. The team is responsible for performing various activities involved in the risk management process. In this process, Cassius was instructed to select and implement appropriate controls on the identified risks in order to address the risks based on their severity level.
Which of the following risk management phases was Cassius instructed to perform in the above scenario?
A. Risk analysis
B. Risk treatment
C. Risk prioritization
D. Risk identification
Nicolas, a computer science student, decided to create a guest OS on his laptop for different lab operations. He adopted a virtualization approach in which the guest OS will not be aware that it is running in a virtualized environment. The virtual machine manager (VMM) will directly interact with the computer hardware, translate commands to binary instructions, and forward them to the host OS.
Which of the following virtualization approaches has Nicolas adopted in the above scenario?
A. Hardware-assisted virtualization
B. Full virtualization
C. Hybrid virtualization
D. OS-assisted virtualization
In an organization, all the servers and database systems are guarded in a sealed room with a single-entry point. The entrance is protected with a physical lock system that requires typing a sequence of numbers and letters by using a rotating dial that intermingles with several other rotating discs.
Which of the following types of physical locks is used by the organization in the above scenario?
A. Digital locks
B. Combination locks
C. Mechanical locks
D. Electromagnetic locks
Leilani, a network specialist at an organization, employed Wireshark for observing network traffic. Leilani navigated to the Wireshark menu icon that contains items to manipulate, display and apply filters, enable, or disable the dissection of protocols, and configure user- specified decodes.
Identify the Wireshark menu Leilani has navigated in the above scenario.
A. Statistics
B. Capture
C. Main toolbar
D. Analyze