300-215 Online Practice Questions and Answers
DRAG DROP
Drag and drop the capabilities on the left onto the Cisco security solutions on the right.
Select and Place:

Which scripts will search a log file for the IP address of 192.168.100.100 and create an output file named parsed_host.log while printing results to the console?
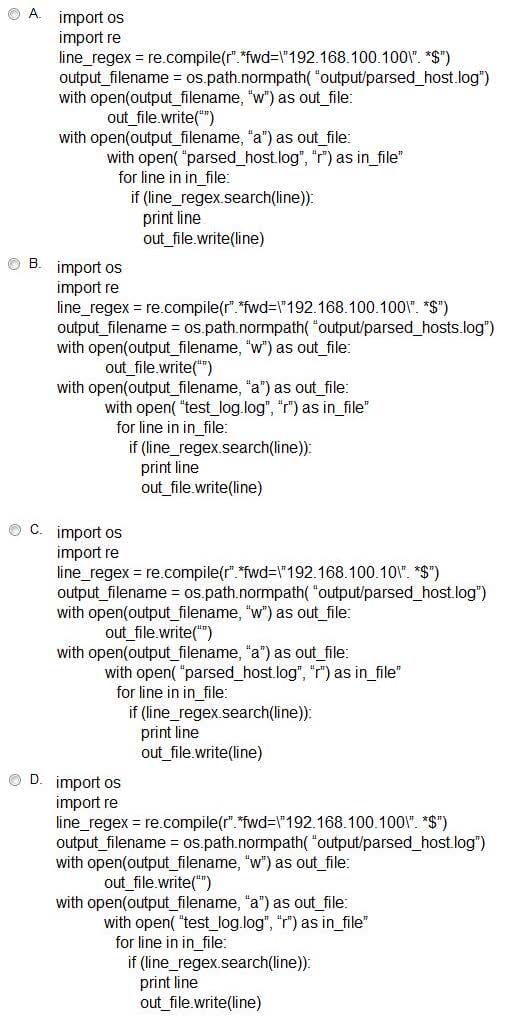
A. Option A
B. Option B
C. Option C
D. Option D

Refer to the exhibit. An engineer is analyzing a .LNK (shortcut) file recently received as an email attachment and blocked by email security as suspicious. What is the next step an engineer should take?
A. Delete the suspicious email with the attachment as the file is a shortcut extension and does not represent any threat.
B. Upload the file to a virus checking engine to compare with well-known viruses as the file is a virus disguised as a legitimate extension.
C. Quarantine the file within the endpoint antivirus solution as the file is a ransomware which will encrypt the documents of a victim.
D. Open the file in a sandbox environment for further behavioral analysis as the file contains a malicious script that runs on execution.

Refer to the exhibit. What is the IOC threat and URL in this STIX JSON snippet?
A. malware; `http://x4z9arb.cn/4712/'
B. malware; x4z9arb backdoor
C. x4z9arb backdoor; http://x4z9arb.cn/4712/
D. malware; malware--162d917e-766f-4611-b5d6-652791454fca
E. stix; `http://x4z9arb.cn/4712/'

Refer to the exhibit. Which type of code is being used?
A. Shell
B. VBScript
C. BASH
D. Python
Which magic byte indicates that an analyzed file is a pdf file?
A. cGRmZmlsZQ
B. 706466666
C. 255044462d
D. 0a0ah4cg
A scanner detected a malware-infected file on an endpoint that is attempting to beacon to an external site. An analyst has reviewed the IPS and SIEM logs but is unable to identify the file's behavior. Which logs should be reviewed next to evaluate this file further?
A. email security appliance
B. DNS server
C. Antivirus solution
D. network device

Refer to the exhibit. According to the Wireshark output, what are two indicators of compromise for detecting an Emotet malware download? (Choose two.)
A. Domain name:iraniansk.com
B. Server: nginx
C. Hash value: 5f31ab113af08=1597090577
D. filename= "Fy.exe"
E. Content-Type: application/octet-stream
An engineer received a report of a suspicious email from an employee. The employee had already opened the attachment, which was an empty Word document. The engineer cannot identify any clear signs of compromise but while reviewing running processes, observes that PowerShell.exe was spawned by cmd.exe with a grandparent winword.exe process. What is the recommended action the engineer should take?
A. Upload the file signature to threat intelligence tools to determine if the file is malicious.
B. Monitor processes as this a standard behavior of Word macro embedded documents.
C. Contain the threat for further analysis as this is an indication of suspicious activity.
D. Investigate the sender of the email and communicate with the employee to determine the motives.
An engineer is analyzing a ticket for an unexpected server shutdown and discovers that the web-server ran out of useable memory and crashed.
Which data is needed for further investigation?
A. /var/log/access.log
B. /var/log/messages.log
C. /var/log/httpd/messages.log
D. /var/log/httpd/access.log

