300-630 Online Practice Questions and Answers
DRAG DROP
A leaf receives unicast traffic that is destined to an unknown source, and spine proxy is enabled in the corresponding bridge domain. Drag and drop the Cisco ACI forwarding operations from the left into the order the operation occurs on the right.
Select and Place:

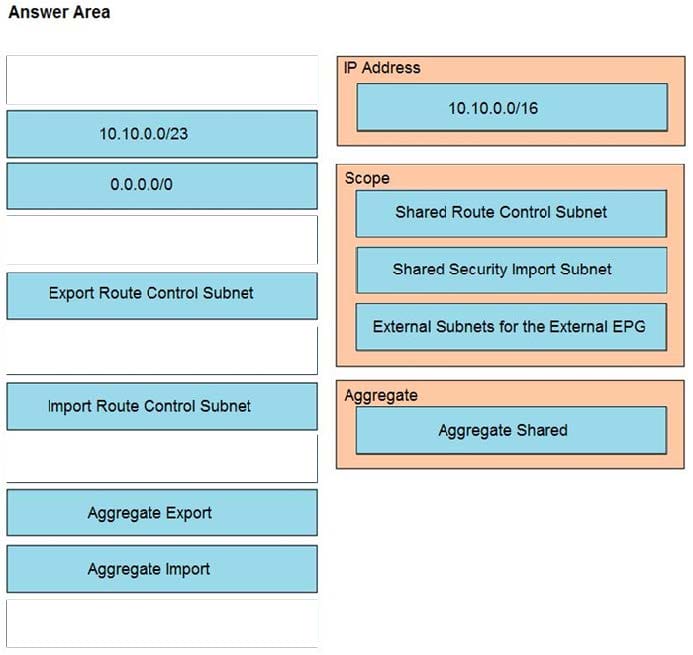
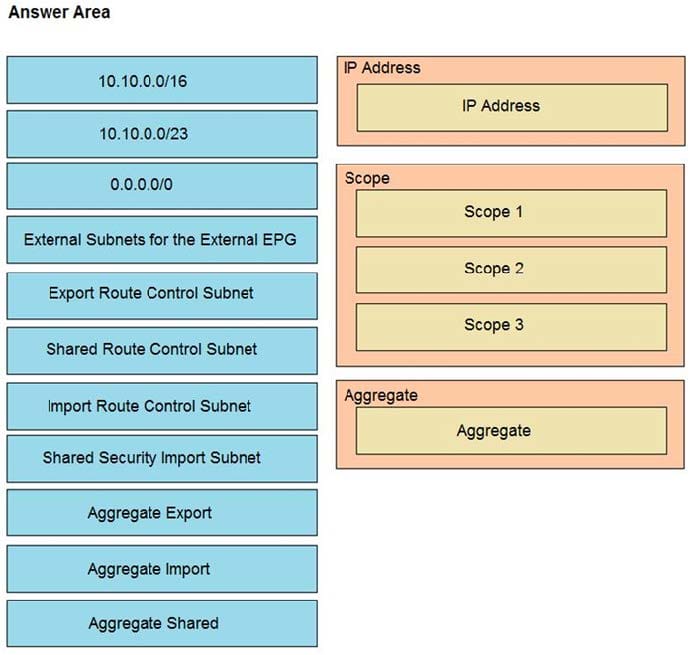
DRAG DROP
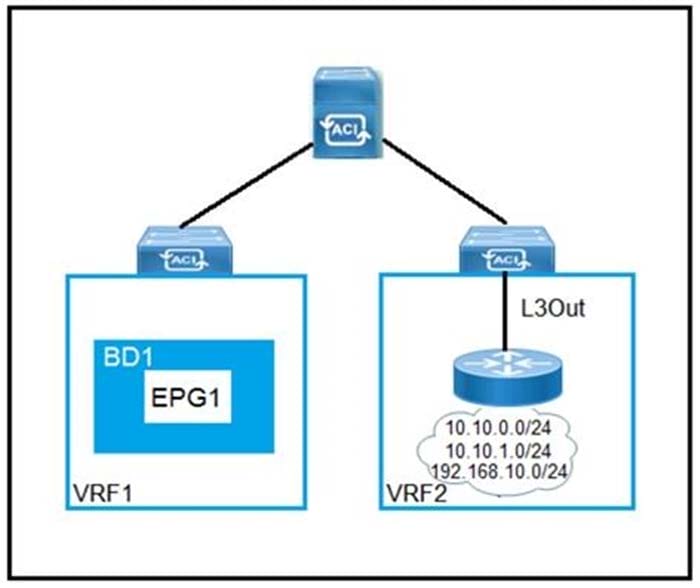
Refer to the exhibit. Drag and drop the subnets and flags from the left into the External Network Instance Profile policies on the right to create a setup that advertises only 10.10.0.0/24 and 10.10.1.0/24 prefixes in VRF1 and establishes connectivity between VRFs. Not all options are used.
Select and Place:
Which two actions are the Cisco best practices to configure NIC teaming load balancing for Cisco UCS B-Series blades that are connected to the Cisco ACI leaf switches? (Choose two.)
A. Create vPC+
B. Enable LACP active mode
C. Create PAgP
D. Create vPC
E. Enable MAC pinning

An organization migrates its virtualized servers from a legacy environment to Cisco ACI. VM1 is incorrectly attached to PortGroup IT|3TierApp|Web. Which action limits IP address learning in BD1?
A. Enable Enforce Subnet Check
B. Enable Rouge Endpoint Control
C. Enable GARP-based EP Move Detection Mode
D. Disable Remote EP Learn
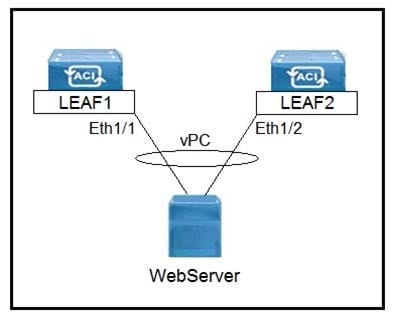
Refer to the exhibit. Which three actions should be taken to implement the vPC in the Cisco ACI fabric? (Choose three.)
A. Select a common vPC interface policy group
B. Select individual interface profiles
C. Select common interface profiles
D. Select individual switch profiles
E. Select common switch profiles
An engineer configures a Cisco ACI Multi-Pod for disaster recovery. Which action should be taken for the new nodes to be discoverable by the existing Cisco APICs?
A. Enable subinterfaces with dot1q tagging on all links between the IPN routers.
B. Configure IGMPv3 on the interfaces of IPN routers that face the Cisco ACI spine.
C. Enable DHCP relay on all links that are connected to Cisco ACI spines on IPN devices.
D. Configure BGP as the underlay protocol in IPN.
An engineer configures a new Cisco ACI Multi-Pod setup. Which action should be taken for fabric discovery to be successful for the nodes in Pod 2?
A. Select the Route Reflector field in Pod Peering
B. Enable the DSCP class-cos translation policy for Layer 3 traffic
C. Configure POD 2 Data Plane TEP under the Pod Connection Profile
D. Add the IPN subnet under the Fabric External Routing Profile
What are two characteristics of Cisco ACI and Spanning Tree Protocol interaction? (Choose two.)
A. When a TCN BPDU is received in a VLAN, Cisco ACI flushes the endpoints for the associated encapsulation.
B. STP BPDUs are dropped due to MCP.
C. MST BPDUs are flooded correctly in Cisco ACI fabric without additional configuration.
D. BPDU filter and BPDU guard can be configured on Cisco ACI leaf edge ports.
E. Cisco ACI must be configured as the STP root for all VLANs.
An engineer deployed a Cisco ACI fabric and noticed that the fabric learns endpoints from subnets that are not configured on a bridge domain. To meet strict security requirements, the engineer must prevent this behavior. Which action must be taken to prevent this behavior?
A. Activate Enable Data Plane Endpoint Learning
B. Implement Pervasive Gateway
C. Configure Static Binding
D. Enable Enforce Subnet Check
Refer to the exhibit.

An engineer is configuring a vSwitch policy in the existing Cisco ACI fabric. The requirement is for the Cisco ACI leaf to learn individual MAC addresses from the same physical port. Which vSwitch policy configuration mode must be enabled to meet this requirement?
A. MAC pinning
B. MAC binding
C. LACP passive
D. LACP active