EC-COUNCIL 412-79V8 Exam Questions & Answers
Want to pass your EC-COUNCIL 412-79V8 exam in the very first attempt? Try Exam2pass! It is equally effective for both starters and IT professionals.
-
Vendor: EC-COUNCIL
Exam Code: 412-79V8
Exam Name: EC-Council Certified Security Analyst (ECSA)
Certification Provider: EC-COUNCIL
Total Questions: 200 Q&A
Updated on: Mar 30, 2025
Note: Product instant download. Please sign in and click My account to download your product. -
- Updated exam questions with all objectives covered
- Verified answers
- 365 days free updates
- 99% success rate
- 100% money back guarantee
- 24/7 customer support
Related Exams
- 112-51 EC-Council Certified Network Defense Essentials (NDE)
- 212-77 EC-Council Certified Linux Security
- 212-81 EC-Council Certified Encryption Specialist (ECES)
- 212-82 EC-Council Certified Cybersecurity Technician (C|CT)
- 212-89 EC-Council Certified Incident Handler (ECIH)
- 312-38 EC-Council Certified Network Defender (CND)
- 312-39 EC-Council Certified SOC Analyst (CSA)
- 312-40 EC-Council Certified Cloud Security Engineer (CCSE)
- 312-49 ECCouncil Computer Hacking Forensic Investigator (V9)
- 312-49V10 EC-Council Certified Computer Hacking Forensic Investigator (V10)
- 312-49V8 EC-Council Certified Computer Hacking Forensic Investigator (V8)
- 312-49V9 EC-Council Certified Computer Hacking Forensic Investigator (V9)
- 312-50 Certified Ethical Hacker
- 312-50V10 EC-Council Certified Ethical Hacker (C|EH v10)
- 312-50V11 EC-Council Certified Ethical Hacker (C|EH v11)
- 312-50V12 EC-Council Certified Ethical Hacker (C|EH v12)
- 312-50V8 Certified Ethical Hacker v8
- 312-50V9 EC-Council Certified Ethical Hacker (C|EH v9)
- 312-75 EC-Council Certified EC-Council Instructor (CEI)
- 312-76 EC-Council Certified Disaster Recovery Professional Practice Test (CEH)
- 312-82 EC-CouncilBlockchain Fintech CertificationB|FC
- 312-85 EC-Council Certified Threat Intelligence Analyst (ECTIA)
- 312-92 EC-Council Certified Secure Programmer v2 (ECSP)
- 312-96 EC-Council Certified Application Security Engineer (CASE) JAVA
- 412-79 EC-Council Certified Security Analyst (ECSA)
- 412-79V10 EC-Council Certified Security Analyst (ECSA) V10
- 412-79V8 EC-Council Certified Security Analyst (ECSA)
- 412-79V9 EC-Council Certified Security Analyst (ECSA) v9
- 512-50 EC-Council Information Security Manager (E|ISM)
- 712-50 EC-Council Certified CISO (CCISO)
Related Certifications
412-79V8 Online Practice Questions and Answers
From where can clues about the underlying application environment can be collected?
A. From the extension of the file
B. From executable file
C. From file types and directories
D. From source code
SQL injection attack consists of insertion or "injection" of either a partial or complete SQL query via the
data input or transmitted from the client (browser) to the web application.
A successful SQL injection attack can:
i)Read sensitive data from the database
iii)Modify database data (insert/update/delete)
iii)Execute administration operations on the database (such as shutdown the DBMS)
iV)Recover the content of a given file existing on the DBMS file system or write files into the file system
v)Issue commands to the operating system
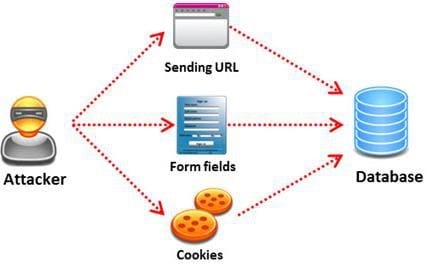
Pen tester needs to perform various tests to detect SQL injection vulnerability. He has to make a list of all input fields whose values could be used in crafting a SQL query, including the hidden fields of POST requests and then test them separately, trying to interfere with the query and to generate an error.
In which of the following tests is the source code of the application tested in a non-runtime environment to detect the SQL injection vulnerabilities?
A. Automated Testing
B. Function Testing
C. Dynamic Testing
D. Static Testing
Amazon, an IT based company, conducts a survey on the usage of the Internet. They found that company employees spend most of the time at work surfing the web for their personal use and for inappropriate web site viewing. Management decide to block all such web sites using URL filtering software.

How can employees continue to see the blocked websites?
A. Using session hijacking
B. Using proxy servers
C. Using authentication
D. Using encryption
Why Choose Exam2pass 412-79V8 Exam PDF and VCE Simulator?
-
100% Pass and Money Back Guarantee
Exam2pass 412-79V8 exam dumps are contained with latest 412-79V8 real exam questions and answers. Exam2pass 412-79V8 PDF and VCE simulator are revised by the most professional 412-79V8 expert team. All the 412-79V8 exam questions are selected from the latest real exam and answers are revised to be accurate. 100% pass guarantee and money back on exam failure.
-
The Most Professional Support Service
Exam2pass has the most skillful 412-79V8 experts. Candidates can get timely help when needed. Exam2pass 412-79V8 exam PDF and VCE simulator are the most up-to-date and valid. The most professional support service are provided to help the 412-79V8 candidates at anytime and anywhere.
-
365 Days Free Update Download
Exam2pass 412-79V8 exam PDF and VCE simulator are timely updated in 365 days a year. Users can download the update for free for 365 days after payment. Exam2pass 412-79V8 exam dumps are updated frequently by the most professional 412-79V8 expert team. 412-79V8 candidates can have the most valid 412-79V8 exam PDF and VCE at any time when needed.
-
Free Demo Download
Download free demo of the Exam2pass exam PDF and VCE simulator and try it. Do not need to pay for the whole product before you try the free trial version. Get familiar about the exam questions and exam structure by trying the free sample questions of the exam PDF and VCE simulator. Try before purchase now!

 Printable PDF
Printable PDF