CSSLP Online Practice Questions and Answers
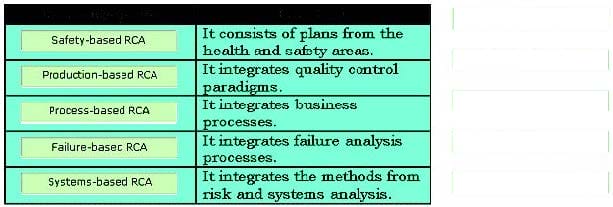
RCA (root cause analysis) is an iterative and reactive method that identifies the root cause of various incidents, and the actions required to prevent these incidents from reoccurring. RCA is classified in various categories. Choose appropriate categories and drop them in front of their respective functions.
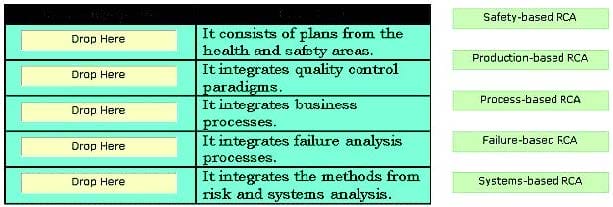
Select and Place:
Which of the following attacks causes software to fail and prevents the intended users from accessing software?
A. Enabling attack
B. Reconnaissance attack
C. Sabotage attack D. Disclosure attack
Which of the following areas of information system, as separated by Information Assurance Framework, is a collection of local computing devices, regardless of physical location, that are interconnected via local area networks (LANs) and governed by a single security policy?
A. Local Computing Environments
B. Networks and Infrastructures
C. Supporting Infrastructures
D. Enclave Boundaries
Which of the following activities are performed by the 'Do' cycle component of PDCA (plan- do- check-act)? Each correct answer represents a complete solution. Choose all that apply.
A. It detects and responds to incidents properly.
B. It determines controls and their objectives.
C. It manages resources that are required to achieve a goal.
D. It performs security awareness training.
E. It operates the selected controls.
Which of the following is a malicious exploit of a website, whereby unauthorized commands are transmitted from a user trusted by the website?
A. Cross-Site Scripting
B. Injection flaw
C. Side channel attack
D. Cross-Site Request Forgery
The service-oriented modeling framework (SOMF) introduces five major life cycle modeling activities that drive a service evolution during design-time and run-time. Which of the following activities integrates SOA software assets and establishes SOA logical environment dependencies?
A. Service-oriented discovery and analysis modeling
B. Service-oriented business integration modeling
C. Service-oriented logical architecture modeling
D. Service-oriented logical design modeling
In which of the following SDLC phases is the system's security features configured and enabled, the system is tested and installed or fielded, and the system is authorized for processing?
A. Development/Acquisition Phase
B. Operation/Maintenance Phase
C. Implementation Phase
D. Initiation Phase
John works as a systems engineer for BlueWell Inc. He has modified the software, and wants to retest the application to ensure that bugs have been fixed or not. Which of the following tests should John use to accomplish the task?
A. Reliability test
B. Functional test
C. Performance test
D. Regression test
Which of the following refers to the ability to ensure that the data is not modified or tampered with?
A. Integrity
B. Availability
C. Non-repudiation
D. Confidentiality
Which of the following components of configuration management involves periodic checks to determine the consistency and completeness of accounting information and to verify that all configuration management policies are being followed?
A. Configuration Identification
B. Configuration Auditing
C. Configuration Control
D. Configuration Status Accounting