GCCC Online Practice Questions and Answers
Which of the following actions would best mitigate against phishing attempts such as the example below?

A. Establishing email filters to block no-reply address emails
B. Making web filters to prevent accessing Google Docs
C. Having employee's complete user awareness training
D. Recommending against the use of Google Docs
How does an organization's hardware inventory support the control for secure configurations?
A. It provides a list of managed devices that should be secured
B. It provides a list of unauthorized devices on the network
C. It provides the MAC addresses for insecure network adapters
D. It identifies the life cycle of manufacturer support for hardware devices
During a security audit which test should result in a source packet failing to reach its intended destination?
A. A new connection request from the Internet is sent to a host on the company 's internal net work
B. A packet originating from the company's DMZ is sent to a host on the company's internal network
C. A new connection request from the internet is sent to the company's DNS server
D. A packet originating from the company's internal network is sent to the company's DNS server
What is the list displaying?
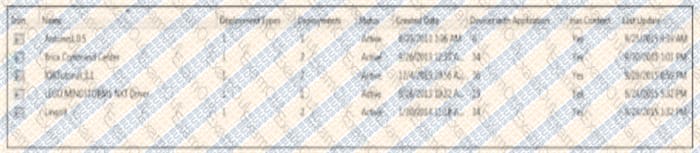
A. Allowed program in a software inventory application
B. Unauthorized programs detected in a software inventory
C. Missing patches from a patching server
D. Installed software on an end-user device
What type of Unified Modelling Language (UML) diagram is used to show dependencies between logical groupings in a system?
A. Package diagram
B. Deployment diagram
C. Class diagram
D. Use case diagram
An organization has created a policy that allows software from an approved list of applications to be installed on workstations. Programs not on the list should not be installed. How can the organization best monitor compliance with the policy?
A. Performing regular port scans of workstations on the network
B. Auditing Active Directory and alerting when new accounts are created
C. Creating an IDS signature to alert based on unknown "User-Agent " strings
D. Comparing system snapshots and alerting when changes are made
According to attack lifecycle models, what is the attacker's first step in compromising an organization?
A. Privilege Escalation
B. Exploitation
C. Initial Compromise
D. Reconnaissance
Why is it important to enable event log storage on a system immediately after it is installed?
A. To allow system to be restored to a known good state if it is compromised
B. To create the ability to separate abnormal behavior from normal behavior during an incident
C. To compare it performance with other systems already on the network
D. To identify root kits included on the system out of the box
Which of the following is a reliable way to test backed up data?
A. Verify the file size of the backup
B. Confirm the backup service is running at the proper time
C. Compare data hashes of backed up data to original systems
D. Restore the data to a system
A global corporation has major data centers in Seattle, New York, London and Tokyo. Which of the following is the correct approach from an intrusion detection and event correlation perspective?
A. Configure all data center systems to use local time
B. Configure all data center systems to use GMT time
C. Configure all systems to use their default time settings
D. Synchronize between Seattle and New York, and use local time for London and Tokyo
