GSLC Online Practice Questions and Answers
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. The company has recently provided laptops to its sales team members. You have configured access points in the network to enable a wireless network. The company's security policy states that all users using laptops must use smart cards for authentication. Select and

place the authentication method you are required to configure to implement the security policy of the company.
Select and Place:

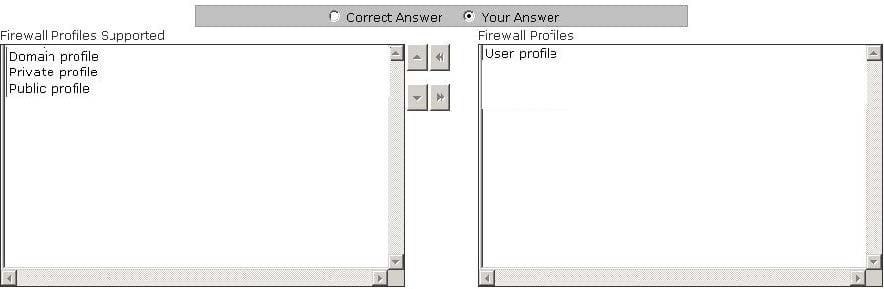
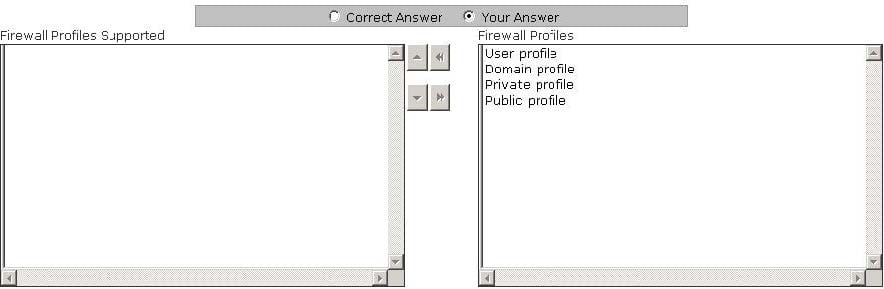
You work as a Network Administrator for Infonet Inc. The company has a Windows Server 2008 domain-based network. The network has three Windows Server 2008 member servers and 150 Windows Vista client computers. According to the company's security policy, you want to apply a firewall profile to the network.Choose the firewall profiles supported by Windows Server 2008 and Windows Vista.
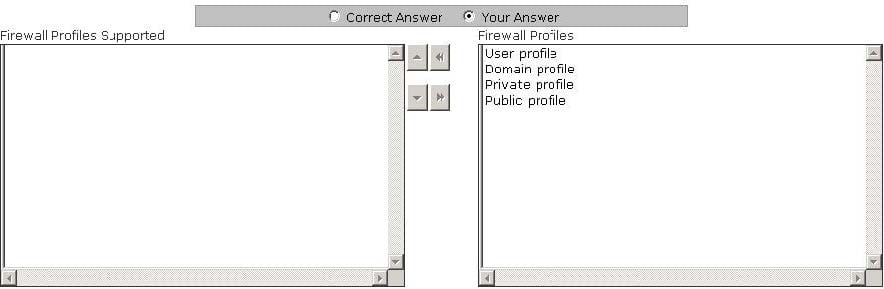
Select and Place:
You are the project manager of a Web development project. You want to get information about your competitors by hacking into their computers. You and the project team determine should the hacking attack not be performed anonymously, you will be traced. Hence, you hire a professional hacker to work on the project. This is an example of what type of risk response?
A. Acceptance
B. Transference
C. Mitigation
D. Avoidance
Which of the following are types of social engineering attacks? Each correct answer represents a complete solution. Choose two.
A. An unauthorized person calls a user and pretends to be a system administrator in order to get the user's password.
B. An unauthorized person inserts an intermediary software or program between two communicating hosts to listen to and modify the communication packets passing between the two hosts.
C. An unauthorized person modifies packet headers by using someone else's IP address to hide his identity.
D. An unauthorized person gains entrance to the building where the company's database server resides and accesses the server by pretending to be an employee.
When following the PIACT process for managing vulnerabilities, which of the following is developed as part of the communication step?
A. Control frameworks
B. Inventories
C. Dashboards
D. Risk analysts
A user has opened a Web site that automatically starts downloading malicious code onto his computer.
What should he do to prevent this?
Each correct answer represents a complete solution. Choose two.
A. Disable ActiveX Controls
B. Disable Active Scripting
C. Implement File Integrity Auditing
D. Configure Security Logs
All of the following are the outputs of the Acquire Project Team process except for which one?
A. Resource calendars
B. Enterprise environmental factors
C. Project staff assignments
D. Project management plan updates
Which of the following statements are true about worms?
Each correct answer represents a complete solution. Choose all that apply.
A. Worms can exist inside files such as Word or Excel documents.
B. Worms cause harm to the network by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer.
C. Worms replicate themselves from one system to another without using a host file.
D. One feature of worms is keystroke logging.
A war dialer is a tool that is used to scan thousands of telephone numbers to detect vulnerable modems. It provides an attacker unauthorized access to a computer. Which of the following tools can an attacker use to perform war dialing? Each correct answer represents a complete solution. Choose all that apply.
A. Wingate
B. ToneLoc
C. THC-Scan
D. NetStumbler
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. John notices that the We-are-secure network is vulnerable to a man-inthe-middle attack since the key exchange process of the cryptographic algorithm it is using does not authenticate participants. Which of the following cryptographic algorithms is being used by the Weare-secure server?
A. RSA
B. Diffie-Hellman
C. Twofish
D. Blowfish