HP0-Y51 Online Practice Questions and Answers
A company has an HP Network Protector SDN Application with these characteristics:
The Network Protector whitelist for all user VLANs includes site1.example.com. The blacklist for all user VLANs includes site1.example.com with a time range
of
9:00 to 17:00.
The Rep DV database includes site1 example.com with a reputation score of 90.
An endpoint attempts to browse to site1.example.com. How does Network Protector classify DNS requests for site1.example.com?
A. It always flags the requests as threats.
B. It flags the requests as threats between 17:00 and 9:00.
C. It flags the requests as threats between 9:00 to 17:00.
D. It never flags the requests as threats.
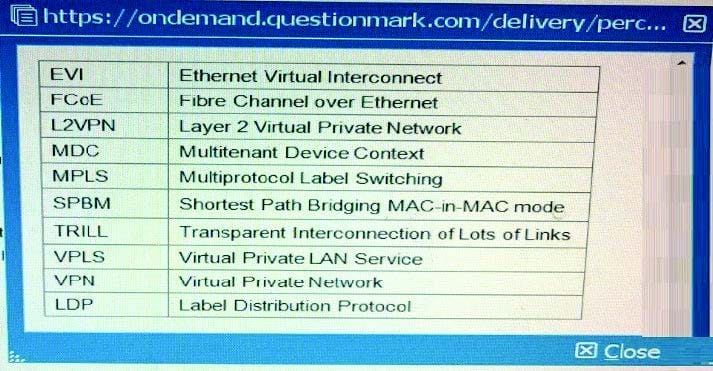
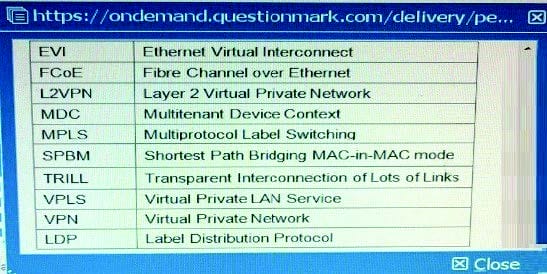
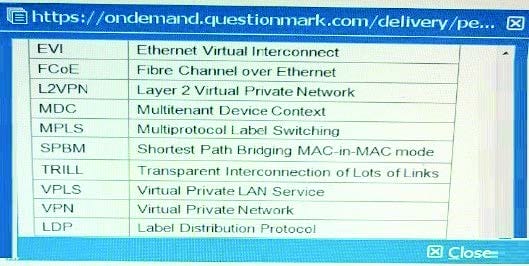
Table of Acronyms

Which common data center requirement does an HP EVI solution meet?
A. It enhances multi-data center solutions by extending Layer 2 connectivity across data centers connected at Layer 3.
B. It provides network administrators with more control over and visibility into communications between virtual machines (VMs).
C. It increases resilience and high availability within a data center transforming Layer 2 connections into a single fabric.
D. It enhances security for communications between data centers by automatically establishing encrypted tunnels between sites.
Table of Acronyms Refer to the exhibit.


An administrator wants to establish a remote LDP session between PE-1 (loopback IP address 10.0 0.1) and PE-2 (loopback IP address; 10.0.0.2). What is required to do this?
A. Both PE-1 and PE-2 have a VPN instance that is defined with the same route distinguisher (RD)
B. Both PE-1 and PE-2 advertise the same label for their loopback IP address
C. Both PE-1 and PE-2 use ordered mode for LDP.
D. Both PE-1 and PE-2 advertise their loopback IP address with OSPF and with LDP.
Table of Acronyms
An administrator is setting up an EVI solution on four HP Comware switches. The switches reach each other on these IP address:
Switch1 = 10.1.1.1
Switch2 = 10 2.2 2
Switch3 = 10.3.3.3
Switch4 = 10.4.4.4
The administrator wants to make Switch1 and Switch2 potential EVI Network Discovery Protocol (ENDP) servers. What is the proper configuration on the Switch1 EVI tunnel interface?
A. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.1.1.1
B. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.2.2.2
C. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
D. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
Which OpenFlow use case is an example of Network Functions Virtualization (NFV)?
A. Use OpenFlow to deploy configurations using IMC VAN SDN Manager.
B. Use OpenFlow to implement a router on an open-vswitch.
C. Use OpenFlow to replace the need of an snmp-agent on the switch.
D. Use OpenFlow to implement traffic prioritization on the edge.
A company has three HP VAN SDN Controllers, which will be deployed in a team. The administrator is deciding whether to create one region or three regions. What is a benefit of creating three regions rather than one region?
A. The team can load balance the team leader role, increasing the total number of RESTful API and Java API calls that the solution can handle.
B. The team can provide high availability for SDN application functions rather than only for the OpenFlow controller functions rather than only for the OpenFlow controller functions.
C. The team can load balance the Master OpenFlow controller role, increasing the total number of packetin messages per second that the solution can handle.
D. The team can provide high availability for all the OpenFlow controller functions rather than only for the SDN application functions.
Table of Acronyms
A company has a data center that hosts multiple tenants. The company is adding a second and third data center switch.
These are the IRF connections:
IRF 1 is the core of the first data center.
IRF 2 is the core of the second data center.
IRF 3 is the core of the third data center
The three data centers are fully interconnected with dark fiber. IRF 1, IRF 2, and IRF 3 have connections to a WAN and to the Internet.
Which option for the connections between the data centers provides the best resiliency and stability?
A. SPBM configured across IRF 1, IRF 2, and IRF 3
B. MSTP running on the links
C. IRF 1, IRF 2, and IRF 3 combined into a single IRF virtual device
D. A link aggregation that consists of all of the links
Table of acronyms
Refer to the exhibit.
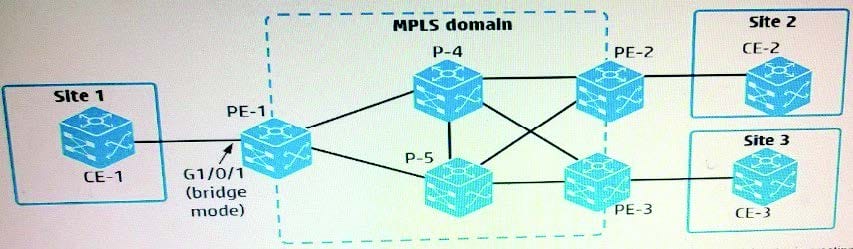
An administrator is setting up an MPLS and L2VPN virtual circuit (VC) between customer Site 1 and Site 2. The administrator is creating a global cross-connect group, which uses LDP signaling, on PE-1. Which two elements are required to do this?
A. An AC connection (specifies a service instance on g1/0/1) and a peer (PE-2)
B. A peer (PE-2) and a VPN instance (associated with g1/0/1)
C. A peer (PE-2) and a VLAN ID (access VLAN or. g1/0/1)
D. An AC connection (specifies a service instance on g1/0/1) and a VPN instance (associated with g1/0/1)
Table of Acronyms

Refer to the exhibit.

An administrator wants to route all external traffic from VPN instances "TenantA" and "TenantB" to a firewall at 10.0.5.5 instance "SharedServices". In addition to setting up the routes between the instances, what is another requirement for this scenario?
A. A router must implement Network Address Translation (NAT) to translate overlapping tenant network addresses.
B. Route leaking must be enabled globally on Router1, as well as on each of the VPN instances.
C. The RAGG 3 interface must be added to VPN instances "TenantA" and "TenantB".
D. Route leaking must be enabled globally on Router1.
Table of Acronyms
Refer to the exhibit.
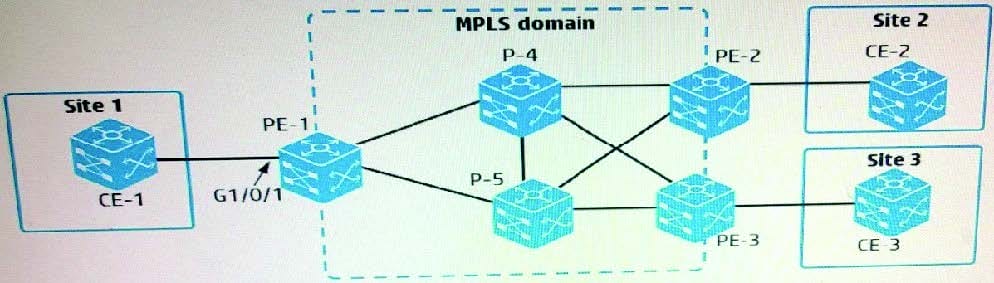
An administrator is setting up MPLS Layer 2 VPN connections between several customer sites:
Connection 1 = Customer site 1 to customer site 2
Connection 2 = Customer site 1 to customer site 3
On PE-1, interface GigabitEthernet1/0/1 connects to CE-1 at site 1. Which setup establishes the desired connections?
A. CE-1 connects to CE-2 in one VLAN, which it assigns to VPN instance 1. It connects to CE-3 in a different VLAN, which it assigns to VPN instance 2. PE-1 instant places G1/0/1 in both VPN instances 1 and 2 and associates each VPN instance with a PW for one of the connections.
B. CE-1 connects to CE-2 in one VLAN and to CE-3 in a different VLAN. PE-1 has two services instances on G1/D/1. One instance encapsulates one VLAN ID and has PW to PE-2, and the other instance encapsulates the other VLAN and has a PW to PE-3
C. PE-1 has two policy-based routing (PBR) policies, each of which selects traffic destined to Site 2 or Site 3. The appropriate policy is applied to the PW for each connection
D. CE-1 implements MPLS. It establishes two PWs with PE-1, one for its connection to CE-2 and one for its connection to CE-3. PE-1 maps the out label for the first PW to the in label for a PW to PE-2. It maps the labels similarly for a PW to PE-3.
