HPE6-A75 Online Practice Questions and Answers
An administrator wants to use Airwave to manually add devices on the network. Where should the administrator perform this action?
A. in Device Setup
B. in Groups
C. in AMP Setup
D. in Devices
Refer to the exhibit.

Based on the configuration for the client's certificate private key as shown, which statements accurately describe the settings? (Select two.)
A. More bits in the private key will increase security.
B. The private key for TLS client certificates is not created.
C. The private key is stored in the ClearPass server.
D. More bits in the private key will reduce security.
E. The private key is stored in the user device.
Which protocol do Mobility Controllers (MCs) use to detect a failed Mobility Master (MM)?
A. VRRP
B. SNMP
C. PAPI
D. IPSec
Refer to the exhibit.

An administrator implements AP licensing on a Mobility Master (MM). Each campus is responsible to purchase its own AP licenses.
There are 900 AP licenses deployed in the global pool
There are three dedicated pools.
From the global pool, 300 AP licenses are assigned to each dedicated pool.
Network engineers at CampusA want to deploy an additional 100 APs. Currently all of the AP licenses in
CampusA and CampusB are allocated, but only 200 of the AP licenses m CampusC are allocated.
What can the administrator do to add capacity for CampusA in alignment with campus policies?
A. Allow CampusA to share from the CampusC pool.
B. Add 100 more AP licenses and assign them to the CampusA pool.
C. Move 100 licenses from the CampusC pool to the global pool.
D. Add 100 more AP licenses to the global pool.
Refer to the exhibit.
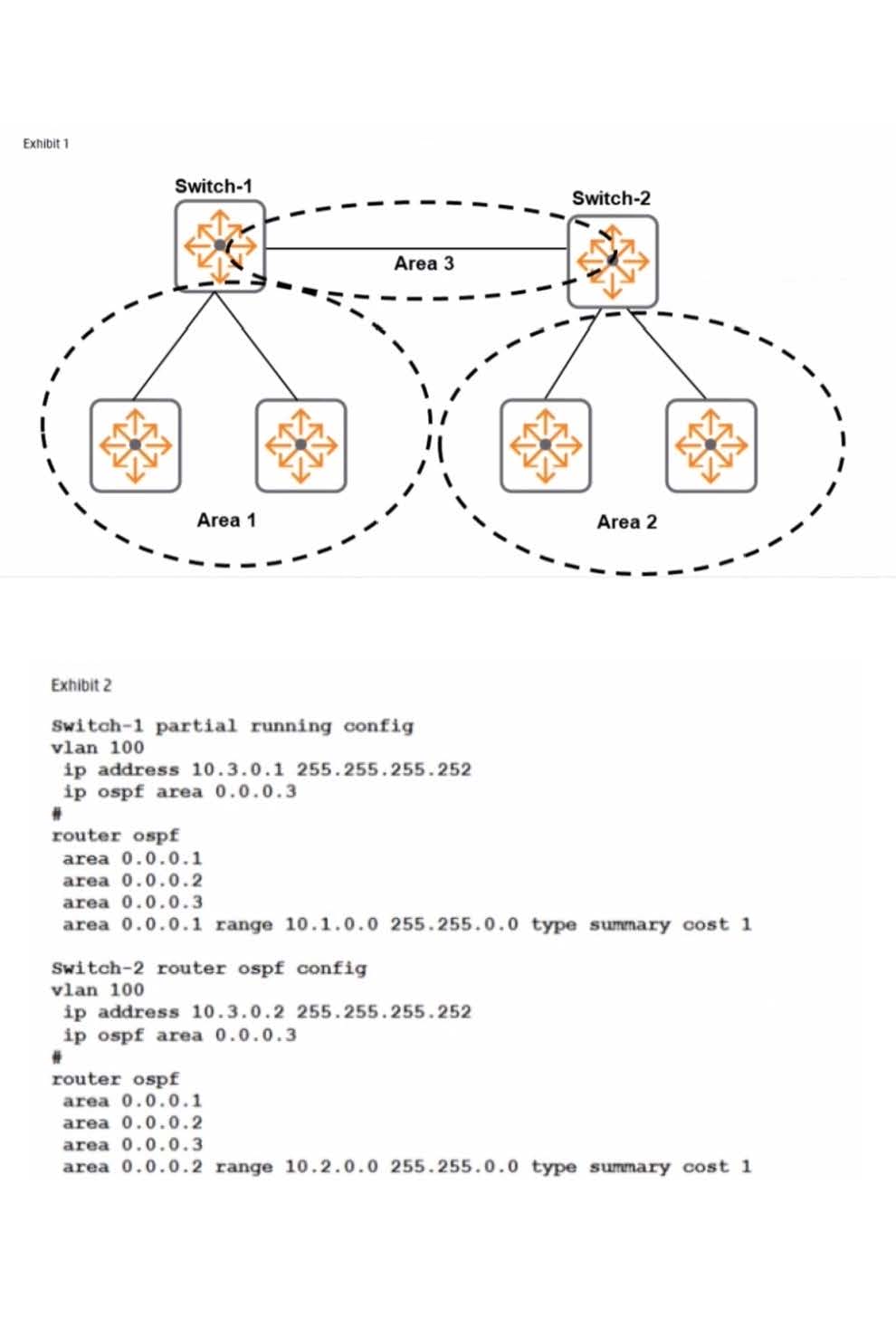
A company has attempted to implement OSPF without success. The devices in Area I need to be able to reach Area 2. Routes should be aggregated for advertisement in other areas. What must be changed to meet these requirements?
A. Change Area 3 to Area 0; remove Area 1 from Switch-2 and Area 2 from Switch-1.
B. Add the 10.2.0.0/16 range on Swttch-1 and the 10.1.0.0/16 range on Switch-2.
C. Add Area 1 and Area 2 on VIAN 100 on both Switch-1 and Switch-2. Remove Area 3.
D. Move the 10.1.0.0/16 range to Area 2 on Switch-1 and the 10.2.0.0/16rangetoArea 1 onSwitch-2.
Refer to the exhibit.
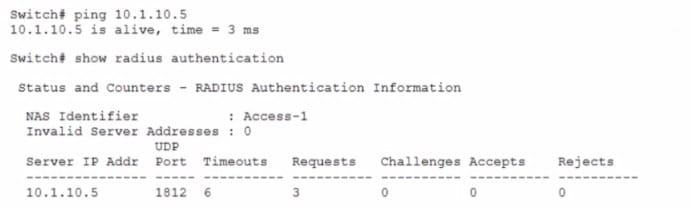
A network administrator sets up 802.1X authentication to a RADIUS server on an AOS- Switch. The
RADIUS server and user devices are both set up to use REAP MSCHAPv2. The administrator tests the authentication and sees the output shown in the exhibit. Which issue could cause this output?
A. The RADIUS shared secret does not match on the switch and the server.
B. The administrator entered the wrong password for the test account.
C. The switch does not have a certificate tor port-access installed on the switch.
D. The switch port is set for user mode 801. IX. but the RADIUS server is set for port mode.
Which statement is true about the databases in ClearPass?
A. Entries in the guest user database do not expire.
B. A Static host list can only contain a list of IP addresses.
C. Entries in the guest user database can be deleted.
D. Entries in the local user database cannot be modified.
E. The endpoints database can only be populated by manually adding MAC addresses to the table.
What is the purpose of the captive portal URL hash key on an AOS-Switch?
A. It authenticates guest users based on the password the users enter hi the portal.
B. It encrypts and secures the RADIUS messages that the AOS-Switch sends to ClearPass.
C. It does not let users alter the URL that redirects them to the portal.
D. It specifies the captive portal URL and conceals the setting in the config.
An administrator needs to authenticate users connected to an ArubaOS Switch where the switch authenticates the user, assigns the firewall policies to the user, and processes some of the users' traffic. Which connection method should the administrator configure on the ArubaOS-Switch?
A. Per-user tunneled node
B. Split-tunneled mode
C. Per-port tunneled node
D. VLAN tunneled mode
An administrator deploys Aruba Mobility Controller 7005s to a company's branch offices. The administrator wants to disable the console port to prevent unauthorized access to the controllers.
Which controller command should the administrator use to implement this policy?
A. no console enable
B. no mgmt-user console
C. mgmt-user console-block
D. console disable
