HPE6-A81 Online Practice Questions and Answers
Refer to the exhibit:



A customer has configured the Aruba Controller for administrative authentication using ClearPass as a TACACS server. During testing, the read-only user is getting the root access role. What could be a possible reason for this behavior? (Select two.)
A. The Controllers Admin Authentication Options Default role is mapped to toot.
B. The ClearPass user role associated to the read-only user is wrong
C. The Controller Server Group Match Rules are changing the user role
D. The read-only enforcement profile is mapped to the root role
E. On the Controller, the TACAC$ authentication server Is not configured for Session authorization
How does the RadSec improve the RADIUS message exchange? (Select two.)
A. It can be used on an unsecured network or the Internet.
B. It builds a TTLS tunnel between the NAD and ClearPass.
C. Only the NAD needs to trust the ClearPass Certificate.
D. It encrypts the entire RADIUS message.
E. It uses UDP to exchange the radius packets.
You have integrated ClearPass Onboard with Active Directory Certificate Services (ADCS) web enrollment
to sign the final device TLS certificates. The customer would also like to use ADCS for centralized
management of TLS certificates including expiration, revocation, and deletion through ADCS.
What steps will you follow to complete the requirement?
A. Remove the EAP-TLS authentication method and add "EAP-TLS with OCSP Enabled' authentication method in the OnBoard Provisioning service. No other configuration changes are required.
B. Copy the [EAP-TLS with OSCP Enabled) authentication method and set the correct ADCS server OCSP URL, remove EAP-TLS and map the custom created method to the Onboard Provisioning Service.
C. Copy the default [EAP-TLS with OSCP Enabled] authentication method and update the correct ADCS server OCSP URL. remove EAP-TLS and map the custom created method to the OnBoard Authorization Service.
D. Edit the [EAP-TLS with OSCP Enabled) authentication method and set the correct ADCS server OCSP URL. remove EAP-TLS and map the [EAP-TLS with OSCP Enabled) method to the Onboard Provisioning Service.
Refer to the exhibit:

When creating a new report, there is an option to send report Notifications by Email. Where is the email server configured?
A. In the ClearPass Policy Manager Endpoint Context servers under Administration.
B. In the Insight Reports Interface under Administration on the sidebar menu.
C. In the insight report on the next screen of the report definition.
D. In the ClearPass Policy Manager Messaging setup under Administration.
Refer to the exhibit:



After the helpdesk revoked the certificate of a device reported to be lost oy an employee, the lost device
was seen as connected successfully to the secure network. Further testing has shown that device
revocation is not working.
What steps should you follow to make device revocations work?
A. Copy the default [EAP-TLS with OSCP Enabled] authentication method and set The Verify certificate using OSCP option as required then update the correct OSCP URL link of the OnBoard CA. Remove EAP-TLS and map the custom created method to the OnBoard Authorization Service.
B. copy the default [EAP-TLS with OSCP Enabled] authentication method and set the verify certificate using OSCP: option as "required" then configure the correct OSCF URL link for the OnBoard CA. Remove EAP-TLS and map the new [EAP-TLS with OSCP Enabled] method to the 802 1X Radius Service.
C. Remove the EAP-TLS authentication method configuration changes are required and add "EAP-TLS with OCSP Enabled" authentication method in the OnBoard Provisioning service. No other configuration changes are required.
D. Edit the default [EAP-TLS with OSCP Enabled] authentication method and set the Verify certificate using OSCP option as required then update the correct OSCP URL link of the OnBoard CA Remove EAP-TLS and map the new [EAP-TLS with OSCP Enabled] method to the OnBoard Provisioning Service.
Refer to the exhibit: A customer has configured a service with the Onboard Devices Repository as an Authentication Source and an Active Directory Domain Server as an Authorization Source. What will happen if the client certificate is still valid and the user account associated with the certificate is disabled in Active Directory?


A. ClearPass will not process the request
B. Enforcement will apply the [Deny Access Profile]
C. ClearPass will redirect the client to Onboard again
D. ClearPass will block network access to the device
E. ClearPass will allow the device to access the network.
Refer to the exhibit:
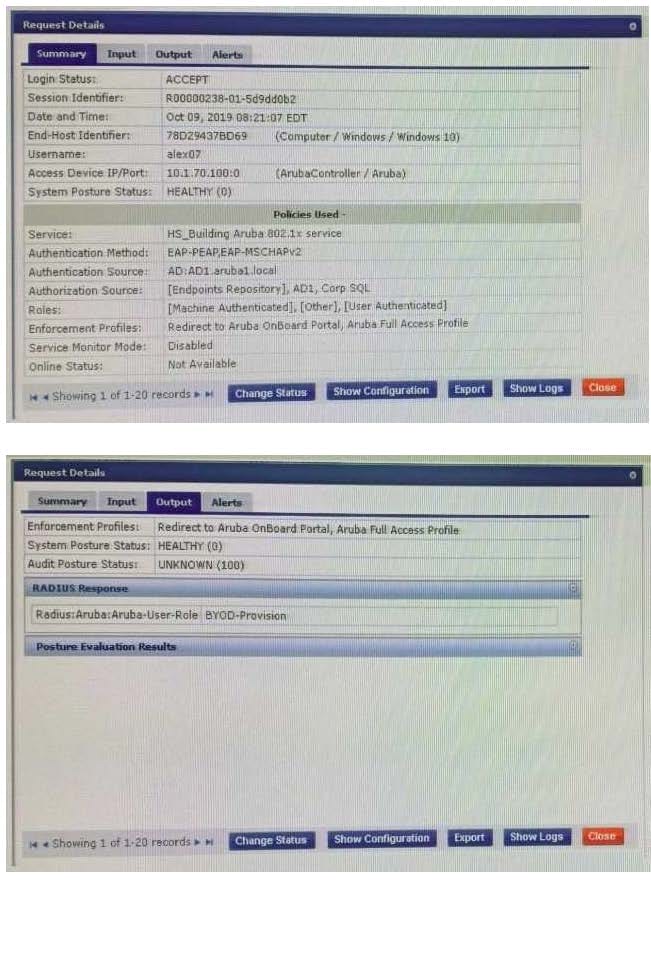
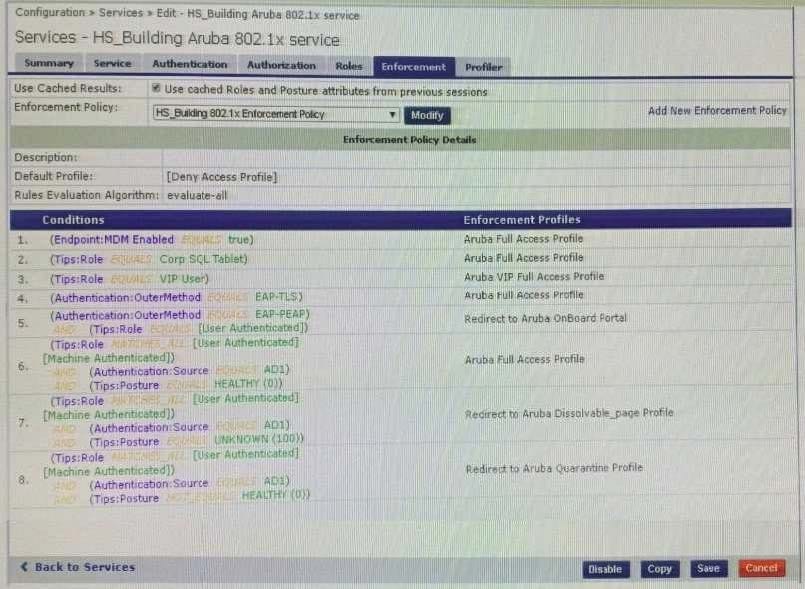
The customer configured an 802.1x service with different enforcement actions for personal and corporate
laptops. The corporate laptops are always being redirected to the BYOD Portal. The customer has sent
you the above screenshots.
How would you resolve the issue? (Select two)
A. Modify the enforcement policy and change the rule evaluation algorithm to select first match
B. Modify the enforcement policy and re-order the condition with posture not_equals to healthy as the sixth condition
C. Modify the enforcement policy and re-order the EAP-PEAP with [user authenticated] rule to the last condition.
D. Modify the enforcement policy and re-order the condition with Posture - Unknown as the fifth condition
E. Remove the EAP-PEAP with [user authenticated] condition for Onboard and create another service
You have Integrated ClearPass Onboard with Active Directory Certificate Services (ADCS) web enrollment to sign the Anal device TLS certificates The Onboard provisioning process completes successfully but when the user finally clicks connect, the user falls to connect to the network with an unknown_ca certificate error. What steps will you follow to complete the requirement?
A. Make sure that the ClearPass servers are using the default self-signed certificates for both SSL and RADIUS server identity
B. Add the ADCS root certificate to both the CPPM Certificate trust list and to the Onboard Certificate Store trust list
C. Make sure both the ClearPass servers have different certificates used for both SSL and RADIUS server identity.
D. Export the self-signed certificate from the ClearPass servers and manually add them as trusted certificates in clients
Refer to the exhibit:




You have been asked to help a Customer troubleshoot an issue. They have configured an Aruba OS
switch (Aruba 2930 with 16.09) to do MAC authentication with profiling using ClearPass as the
authentication source. They cannot get it working.
Using the screenshots as a reference, how will you fix the issue?
A. Delete the initial role in the Aruba OS switch to force the device to get the server derived user roles
B. Use a CoA to bounce the switch port to force the port to change to the correct Aruba user role
C. Change the Vendor settings for the Aruba OS switch to "Aruba" so that the enforcement will use the correct VSAs
D. Modify the enforcement profile conditions with Aruba Vendor specific attributes and Aruba-user- roles
E. User-roles are case sensitive, update the correct role with correct case in the enforcement profile
What type of EAP certificate are you able to use on ClearPass? (Select two.)
A. Self signed, when all the clients are Onboarded with the same Root CA as the Self signed certificate.
B. Private signed, when the clients are onboarded or are part of the organization domain.
C. Private signed, when some clients are onboarded and some are not part of the organization.
D. Public signed, when not all of the clients are part of the organization domain.
E. Self signed, when all the clients are part of the organization domain.
