ITILSC-OSA Online Practice Questions and Answers
Scenario
Vericom is a leading provider of government, business and consumertelecommunication services, and is
currently seeking ways in which toimprove its utilization of IT services to drive growth across its'
multiplelines of business. One of the largest organizations in the UnitedKingdom, Vericom is comprised of
the following business units:
Verinet (providing ADSL, cable, 3GSM, dialup and satellite services) Infrastructure Services (planning,
installing and maintaining the PSTN and mobile network infrastructure)
VericomTV (Pay TV)
Consumer Sales and Marketing (including 400 Vericom retailoutlets) Business and Government
Finance and Administration
Information Technology Services (Shared Service Unit, however some business units also have their own
internal service provider) Human Resources
Vericom Wholesale (for wholesale of Vericom infrastructureservices)
Due to the extensive scope of infrastructure deployed and largeemployee and customer base, Vericom
continues to rely on legacysystems for some critical IT services; however this is seen as abarrier to future
organizational growth and scalability of servicesoffered. The CIO of Vericom has also raised the concern
that whileimprovements to the technology utilized is important, this also needsto be supported by quality IT Service Management practicesemployed by the various IT departments. The project of improving the IT Service Management practicesemployed by Vericom has been outsourced to external consultantswho are aware of the major IT refresh that is going to be occurringover the next 24 months.
Refer to the scenario.
Discussions have recently been held regarding the performance ofthe Incident and Problem Management. There has been someconfusion among IT managers as to what metrics demonstrate thequality and performance of these two processes.
From the options below, which represents the best range ofmeasures for evaluating the success of Incident and ProblemManagement?
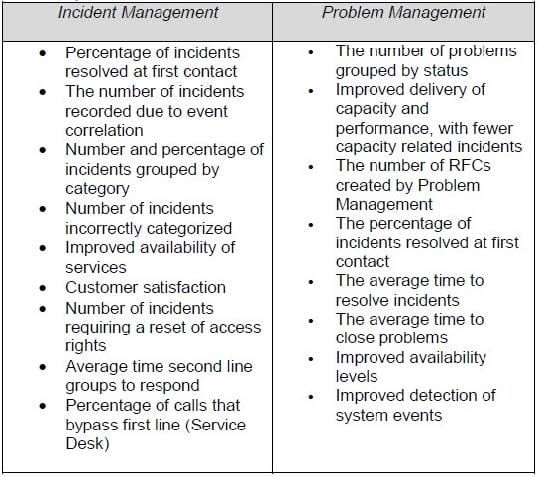
A.
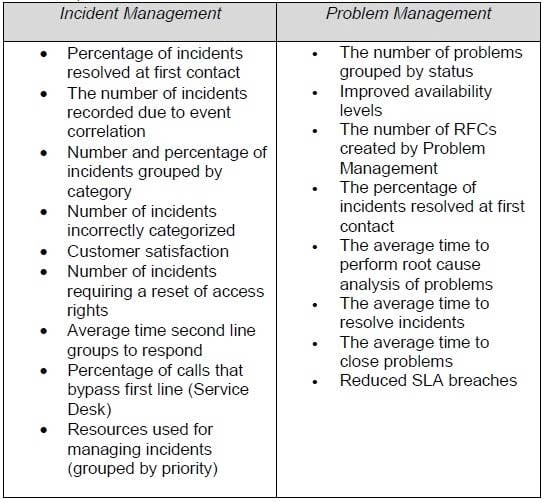
B.
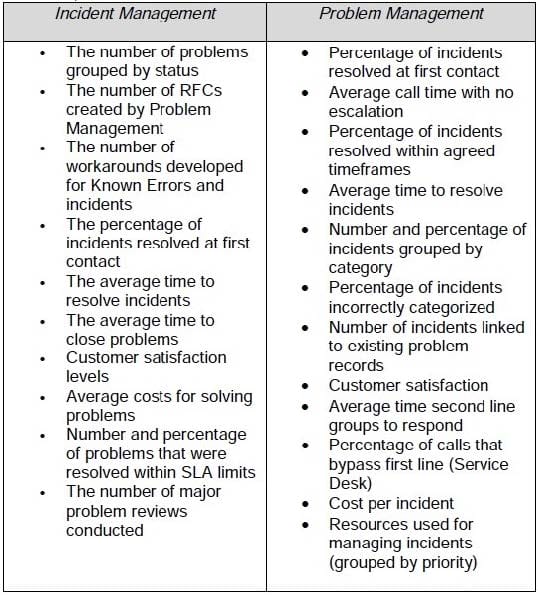
C.
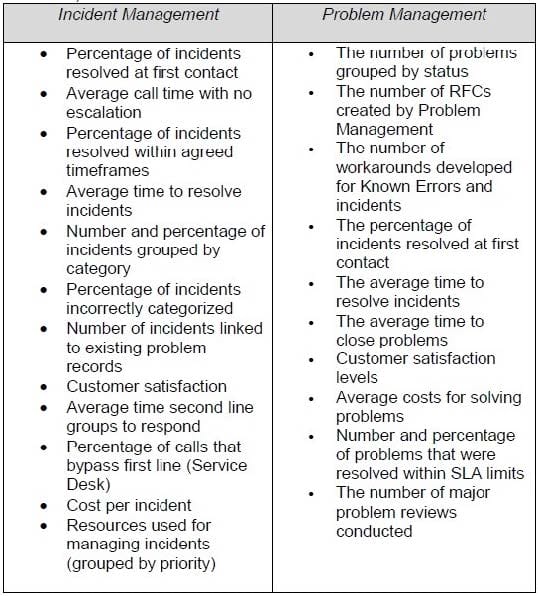
D.
Scenario
Vision Media is an international media organization, operating variouslines of business including:
Film Production Television (production and delivery of their own channel in the United States VisionOne) Print media (including newspapers in 15 countries) Online Advertising
The organization has recently been restructured, and now iscomprised of the following companies and departments:
Vision Films (production of movies and television shows) VisionOne (television channel) VisionNews (coordinates all of the sub-companies involved in the delivery of printed newspapers, as well as being the centralized source of news information for all company owned media outlets) VisionNet (managing the online and internet businesses) Legal Services Finance and Administration Human Resources Information Technology
The organization is also actively pursuing growth in the online market,and is currently holding discussions with the leading online newsprovider about the possible acquisition of their company. This wouldincrease the overall size of Vision Media by around 15%.
The Information Technology department acts as a Shared ServiceUnit, providing IT Services to all of sub-companies and departments,which complement some of the Internal Service Providers that alsoexist. The director of Information Technology has realized the need toimprove the quality of services offered by implementing ITIL, and hasdecided to do so using a phased approach. Some of the ServiceDesign and Service Transition processes have already beenimplemented, and they are now planning the implementation ofService Operation.
While the IT director does have tentative support from the otherdirectors and CEO, budgets for implementing the Service Operationprocesses have not been finalized, and still require a business caseto be formally submitted.
There is some confusion as to how the process of AccessManagement should be designed. In particular, there is debate as tohow the process should be integrated into the overall approach of ITService Management within Vision Media. The IT director has askedfor submissions from some of her staff, describing how they thinkAccess Management should be designed.
Which of the following submissions describes the most appropriateway in which to design and implement Access Management withinVision Media?
A. The design of a quality Access Management process will need toconsider the current state of IT Service Management that exists withinthe IT department, as well as the organizational requirements ofVision Media in general. This will require interfaces to be createdwith: Information Security Management: Which is responsible forthe development and renewal of security policies, guidelinesand procedures, which are then executed by AccessManagement Service Level Management: Which is responsible defining thecustomer requirements for access to IT services Request Fulfillment: Access Management will often betriggered by Service Requests, taken by the Service Desk orsubmitted using automated and self-help mechanisms Change Management: Request for Changes (RFCs) will ofteninvolve modification of access rights Demand Management: Which will provide information as tothe patterns of business that will generate requests foraccess. Outside the scope of IT Service Management, some of the interfacesthat will also need to be created are: Human Resources: So that effective (and automated)communication exists to assist in the creation, modification,removal and audit of access rights. General: Direct requests from department managers Requests for enabling increased access for VIP staff
B. The design of an efficient Access Management process will need toaccount for the existing IT Service Management processes alreadyimplemented within the IT department, as well as the HumanResource requirements of Vision Media in general. This will requireinterfaces to be created with: Information Security Management: Which is responsible forthe development and renewal of security policies, guidelinesand procedures, which are then executed by AccessManagement Capacity Management: Which is responsible for the design ofsystems and infrastructure, which are in turn supported byAccess Management Knowledge Management: Each Knowledge base will requirevarious levels of access to be defined and enforced. Change Management: Request for Changes (RFCs) will ofteninvolve modification of access rights Demand Management: Which will provide information as tothe patterns of business thatwill generate requests foraccess Outside the scope of IT Service Management, some of the interfaces that will also need to be created are: Legal Services: So that the Legal department can verify the request for access is appropriate and lawful. ?General: Direct requests from department managers Requests for enabling increased access for VIP staff
C. It is important that the implementation of Access Managementconsiders a number of key interfaces with existing IT ServiceManagement processes, as well as other business processes, toensure success and satisfaction of its defined objectives. Thisincludes: Information Security Management: Which is responsible forthe development and renewal of security policies, guidelinesand procedures, which are then executed by AccessManagement Availability Management: Which is responsible for the designof security systems and infrastructure, which are in turnsupported by Access Management Request Fulfillment: Access Management will often betriggered by Service Requests, taken by the Service Desk orsubmitted using automated and self-help mechanisms Change Management: Request for Changes (RFCs) will ofteninvolve modification of access rights Configuration Management: Which can be used to recordrelationships between users and systems they can access. Outside the scope of IT Service Management, some of the interfaces that will also need to be created are: Human Resources: So that effective (and automated) communication exists to assist in the creation, modification, removal and audit of access rights. General: Direct requests from department managers Requests for enabling restricted access to contractorsand external suppliers
D. Access Management will need to be implemented in isolation fromexisting IT Service Management processes already in place at VisionMedia so that its' integrity can be ensured. The only exception to thisis Information Security Management, which is responsible for thedevelopment and renewal of security policies, guidelines andprocedures. Access Management uses these as formal inputs, whichare then executed accordingly.
Scenario
Vision Media is an international media organization, operating variouslines of business including:
Film Production Television (production and delivery of their own channel in the United States VisionOne) Print media (including newspapers in 15 countries) Online Advertising
The organization has recently been restructured, and now iscomprised of the following companies and departments:
Vision Films (production of movies and television shows) VisionOne (television channel) VisionNews (coordinates all of the sub-companies involved in the delivery of printed newspapers, as well as being the centralized source of news information for all company owned media outlets) VisionNet (managing the online and internet businesses) Legal Services Finance and Administration Human Resources Information Technology
The organization is also actively pursuing growth in the online market,and is currently holding discussions with the leading online newsprovider about the possible acquisition of their company. This wouldincrease the overall size of Vision Media by around 15%.
The Information Technology department acts as a Shared ServiceUnit, providing IT Services to all of sub-companies and departments,which complement some of the Internal Service Providers that alsoexist. The director of Information Technology has realized the need toimprove the quality of services offered by implementing ITIL, and hasdecided to do so using a phased approach. Some of the ServiceDesign and Service Transition processes have already beenimplemented, and they are now planning the implementation ofService Operation.
While the IT director does have tentative support from the otherdirectors and CEO, budgets for implementing the Service Operationprocesses have not been finalized, and still require a business caseto be formally submitted.
Refer to the exhibit.
The IT director is now considering the implementation of the ServiceOperation functions. However there seems to be overlap between thegoals and objectives for each of the functions, which is causing someconcern among staff involved in the project. Which of the following responses BEST describes the objectives ofthe four Service Operation functions?

A.

B.

C.

D.
Scenario
Vision Media is an international media organization, operating variouslines of business including:
Film Production Television (production and delivery of their own channel in the United States VisionOne) Print media (including newspapers in 15 countries) Online Advertising The organization has recently been restructured, and now iscomprised of the following companies and departments:
Vision Films (production of movies and television shows) VisionOne (television channel) VisionNews (coordinates all of the sub-companies involved in the delivery of printed newspapers, as well as being the centralized source of news information for all company owned media outlets) VisionNet (managing the online and internet businesses) Legal Services Finance and Administration Human Resources Information Technology
The organization is also actively pursuing growth in the online market,and is currently holding discussions with the leading online newsprovider about the possible acquisition of their company. This wouldincrease the overall size of Vision Media by around 15%.
The Information Technology department acts as a Shared ServiceUnit, providing IT Services to all of sub-companies and departments,which complement some of the Internal Service Providers that alsoexist. The director of Information Technology has realized the need toimprove the quality of services offered by implementing ITIL, and hasdecided to do so using a phased approach. Some of the ServiceDesign and Service Transition processes have already beenimplemented, and they are now planning the implementation ofService Operation.
While the IT director does have tentative support from the otherdirectors and CEO, budgets for implementing the Service Operationprocesses have not been finalized, and still require a business caseto be formally submitted.
Refer to the exhibit.
Sally Robbins, who had previously managed the IT department'sService Desk, has now been assigned the role of Incident Manager.To assist in the implementation of the process, Sally has conducted anumber of meetings with IT staff, customers, external suppliers andother relevant stakeholders to identify their requirements. Based onthese discussions, Sally has created following impact definitions,which will be used in conjunction to the given urgency to determinethe appropriate timescales and effort applied for response andresolution to recorded incidents.

Impact Definition: Low Impact Affects a single user, preventing them from performingnormal work functions A single, non-critical device
or peripheral is unavailable Medium Impact
Multiple users are affected, preventing them fromperforming normal work functions A regular business function is unavailable to part of aor organizational unit department
High Impact
A vital business function is unavailable to an entiredepartment or company owned organization
Major Incident
A vital business function is unavailable to all Vision Media departments and company owned organizations
Example Incidents:
I. The IT manager of Vision Films detects that their dedicatedVirtual Private Network linking them to Vision Media'scorporate IT systems has failed. This has prevented usersfrom accessing or modifying any file, document or systemmaintained by the centralized IT department of Vision Media.
II. The vice-president of the Finance and Administrationdepartment reports that her laptop keeps rebooting. She hasan important report to complete for the Chief ExecutiveOfficer.
III. The president of Vision TV is unable to stream high-definitionvideo from a regional office. He requires the regional office'sWAN connection to be upgraded to a 14.4 M/bit wirelessmobile network.
IV. A IT staff member is alerted to the failure of systems providedby Human Resources to all other departments and subcompaniesto manage payments and leave for Vision Mediaemployees (and those employed by organizations fully ownedby Vision Media)
Which of the following responses provides the correct assignment ofimpact to the above incidents?
A. High Impact
II. Medium Impact
III. Not an incident, should be a Request for Change
IV. Major Incident
B. High Impact
II. Low Impact
III. Not an incident, should be a Request for Change
IV. Major Incident
C. Major Incident
II. Medium Impact
III. High Impact
IV. Major Incident
D. High Impact
II. Low Impact
III. Medium Impact
IV. Major Incident
Technical Management is NOT responsible for?
A. Maintenance of the technical Infrastructure
B. Documenting and maintaining the technical skills required to manage and support the IT Infrastructure
C. Defining the Operational Level Agreements for the various technical teams
D. Diagnosis of, and recovery from, technical failures
There have been multiple incidents recorded by the Service Desk. Itappears that the network is congested due to multiple connections.
What kind of actions should the Service Desk analyst take in thisinstance?
A. They should ask the Capacity Manager to expand the capacity of the network
B. They should ask the Problem Manager to look into the problem right away
C. They should ask the Security Manager to check whether too many authorizations may have been issued.
D. They should ask the Service Level Manager to revise the Service Level Agreements (SLA) with a decreased availability target
Which of the following is NOT an example of a Service Request?
A. A user calls the Service Desk to order a toner cartridge
B. A user calls the Service Desk because they would like to change the functionality of an application.
C. A Manager submits a request for a new employee to be given access to an application
D. A user logs onto an internal web site to download a licensed copy of software from a list of approved options
Which ITIL process ensures that the IT Services are restored as soonas possible in the case of a malfunction?
A. Change Management
B. Incident Management
C. Problem Management
D. Service Level Management
Operations Control refers to?
A. The managers of the Event and Access Management Processes
B. Overseeing the monitoring and escalating of IT operational events and activities
C. The tools used to monitor the status of the IT Network
D. The situation where the Service Desk manager is required to monitor the status of the infrastructure when Service Desk Operators are not available
What is the best definition of an Incident Model?
A. A type of incident involving an authorized Configuration Item (CI)
B. The template used by Service Desk analysts to record incidents
C. A set of pre-defined steps to be followed when dealing with a known type of incident
D. An Incident that is easy is solved at first contact
