SC-100 Online Practice Questions and Answers
HOTSPOT
You have a Microsoft 365 E5 subscription and an Azure subscription.
You need to evaluate the existing environment to increase the overall security posture for the following components:
1.
Windows 11 devices managed by Microsoft Intune
2.
Azure Storage accounts
3.
Azure virtual machines
What should you use to evaluate the components? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:

HOTSPOT
You need to recommend a solution to meet the compliance requirements.
What should you include in the recommendation? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:

HOTSPOT
You are evaluating the security of ClaimsApp.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:

After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your on-premises network contains an e-commerce web app that was developed in Angular and Node,js. The web app uses a MongoDB database. You plan to migrate the web app to Azure. The solution architecture team proposes the following architecture as an Azure landing zone.
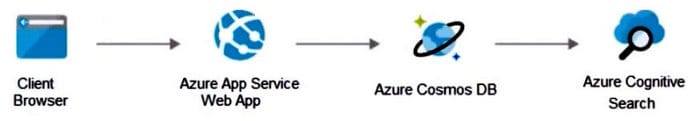
You need to provide recommendations to secure the connection between the web app and the database. The solution must follow the Zero Trust model.
Solution: You recommend creating private endpoints for the web app and the database layer.
Does this meet the goal?
A. Yes
B. No
Your company has a Microsoft 365 E5 subscription.
The company plans to deploy 45 mobile self-service kiosks that will run Windows 10.
You need to provide recommendations to secure the kiosks. The solution must meet the following requirements:
1.
Ensure that only authorized applications can run on the kiosks.
2.
Regularly harden the kiosks against new threats.
Which two actions should you include in the recommendations? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. Implement Automated investigation and Remediation (AIR) in Microsoft Defender for Endpoint.
B. Onboard the kiosks to Microsoft intune and Microsoft Defender for Endpoint.
C. Implement threat and vulnerability management in Microsoft Defender for Endpoint.
D. Onboard the kiosks to Azure Monitor.
E. Implement Privileged Access Workstation (PAW) for the kiosks.
You have an Azure subscription that contains several storage accounts. The storage accounts are accessed by legacy applications that are authenticated by using access keys.
You need to recommend a solution to prevent new applications from obtaining the access keys of the storage accounts. The solution must minimize the impact on the legacy applications.
What should you include in the recommendation?
A. Apply read-only locks on the storage accounts.
B. Set the AllowSharcdKeyAccess property to false.
C. Set the AllowBlobPublicAcccss property to false.
D. Configure automated key rotation.
You have Microsoft Defender for Cloud assigned to Azure management groups.
You have a Microsoft Sentinel deployment.
During the triage of alerts, you require additional information about the security events, including suggestions for remediation.
Which two components can you use to achieve the goal? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
A. Microsoft Sentinel threat intelligence workbooks
B. Microsoft Sentinel notebooks
C. threat intelligence reports in Defender for Cloud
D. workload protections in Defender for Cloud
Your company has a Microsoft 365 subscription and uses Microsoft Defender for Identity.
You are informed about incidents that relate to compromised identities.
You need to recommend a solution to expose several accounts for attackers to exploit. When the attackers attempt to exploit the accounts, an alert must be triggered.
Which Defender for Identity feature should you include in the recommendation?
A. sensitivity labels
B. custom user tags
C. standalone sensors
D. honeytoken entity tags
For a Microsoft cloud environment, you are designing a security architecture based on the Microsoft Cloud Security Benchmark.
What are three best practices for identity management based on the Azure Security Benchmark? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
A. Manage application identities securely and automatically.
B. Manage the lifecycle of identities and entitlements
C. Protect identity and authentication systems.
D. Enable threat detection for identity and access management.
E. Use a centralized identity and authentication system.
You need to recommend a solution to meet the security requirements for the virtual machines. What should you include in the recommendation?
A. an Azure Bastion host
B. a network security group (NSG)
C. just-in-time (JIT) VM access
D. Azure Virtual Desktop



